Read why top brands are personalizing CX to lead their industries, and how your organization can deliver these engaging and unique experiences to every customer.
Real-time next best experience
Real-time next best experience



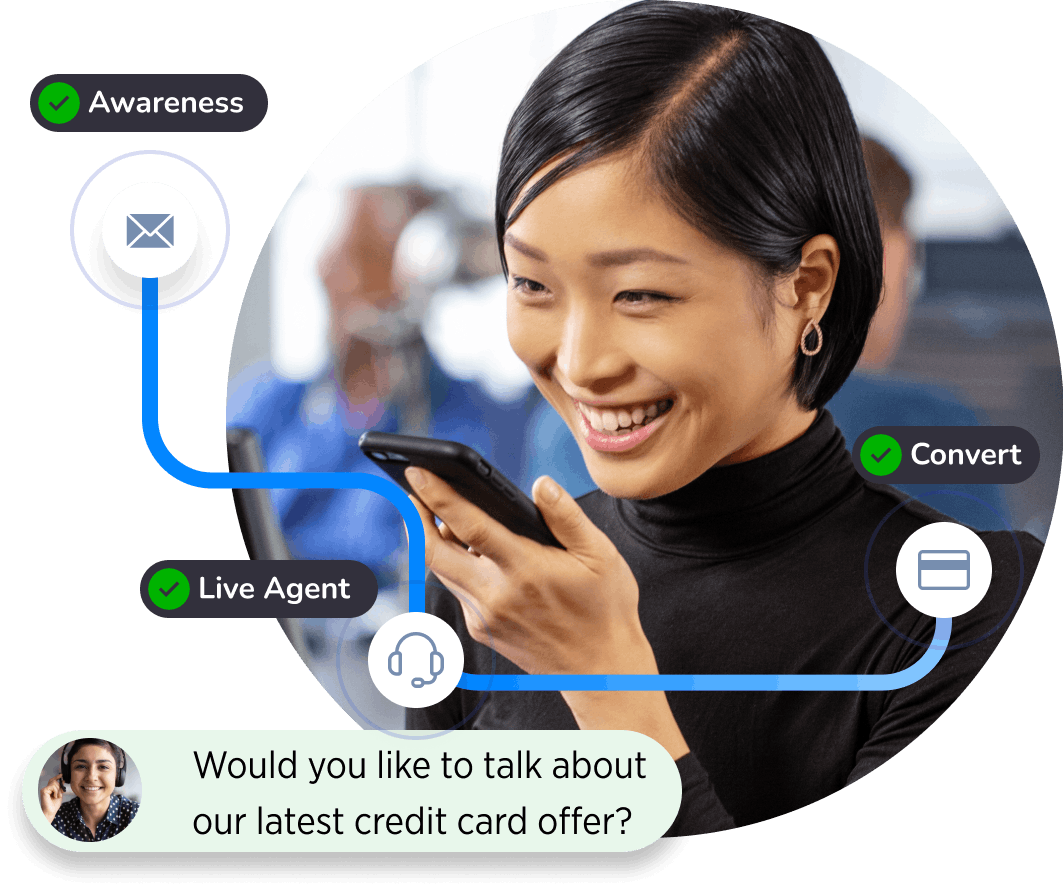
Medallia Experience Orchestration (MXO) extends customer experience insight into actionable strategies by identifying real-time customer intent, then applying what is learned to make every action the right action for every customer moment.
Enable brands to understand the dynamic needs of each customer to then tailor action in the moment and deliver effortless engagement
Listen to customers anonymous online activity to discover interest, and understand context to deliver relevant and valuable conversations
Dynamically manage simple resolutions enabling operational teams to handle and focus on mission critical interactions
In this video, you’ll see a step-by-step process for how Medallia Experience Orchestration can help you turn your CX program from a cost center into a profit center.
In this video, you’ll see a step-by-step process for how Medallia Experience Orchestration can help you turn your CX program from a cost center into a profit center.

“MXO led to insights that fundamentally changed the way we understand how customers interact with our brands. With Medallia, we are stronger, generating higher conversions and increased NPS.”
Mesut Ocalan
Head of Analytics – Global D2C, BSH Hausgerate
Guiding personalized experiences — no matter where the customer shows up — starts with putting the customer first. Activate your individualized experience insights gathered in Medallia Experience Cloud to deliver seamless, end-to-end experiences.
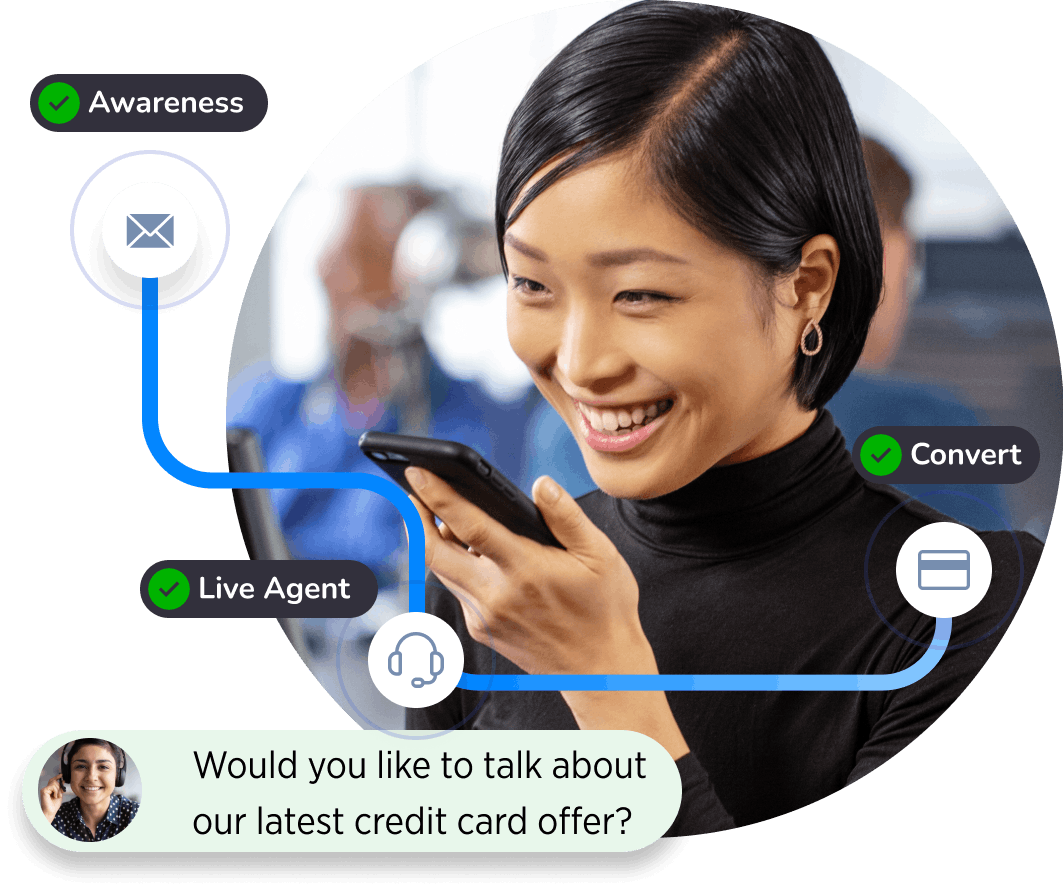
Uncover a unique perspective into customer journeys with powerful visualizations and behavioral insights. Improve the end-to-end experience by identifying critical moments across all channels of engagement.
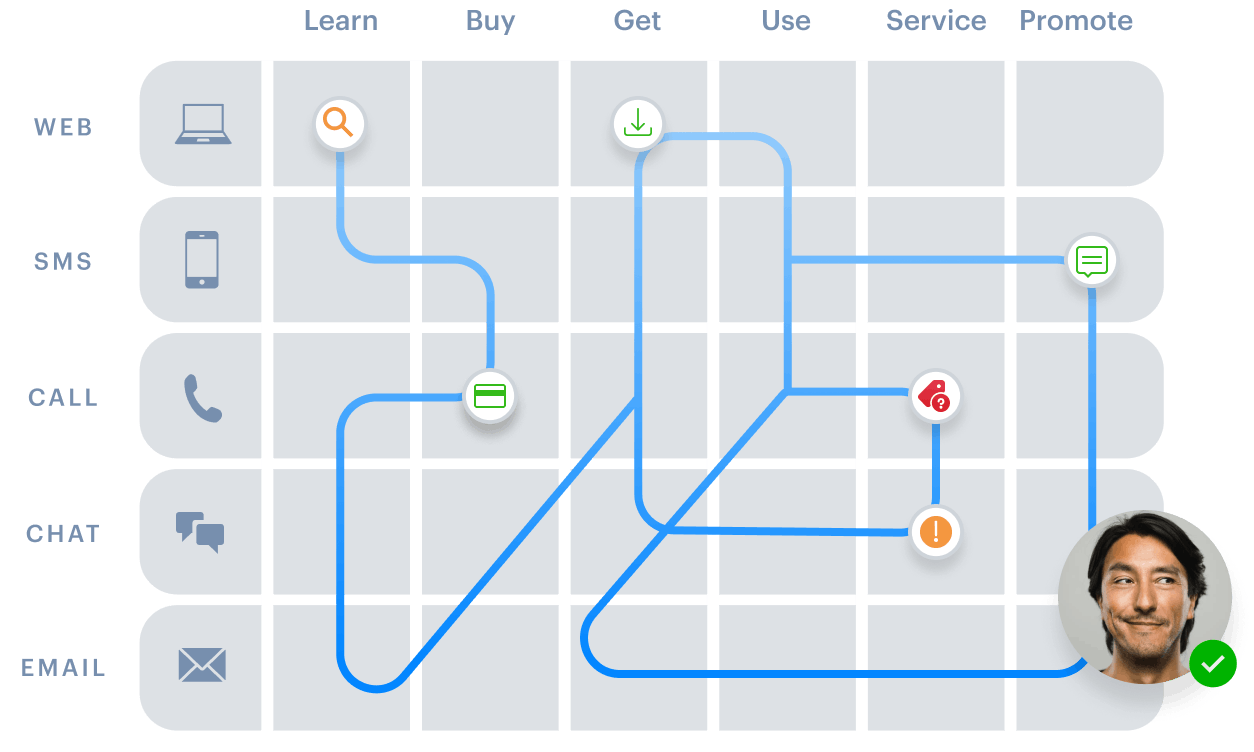
Orchestrate experiences in the moment with up to the second insights to deliver individualized interactions that build brand loyalty.
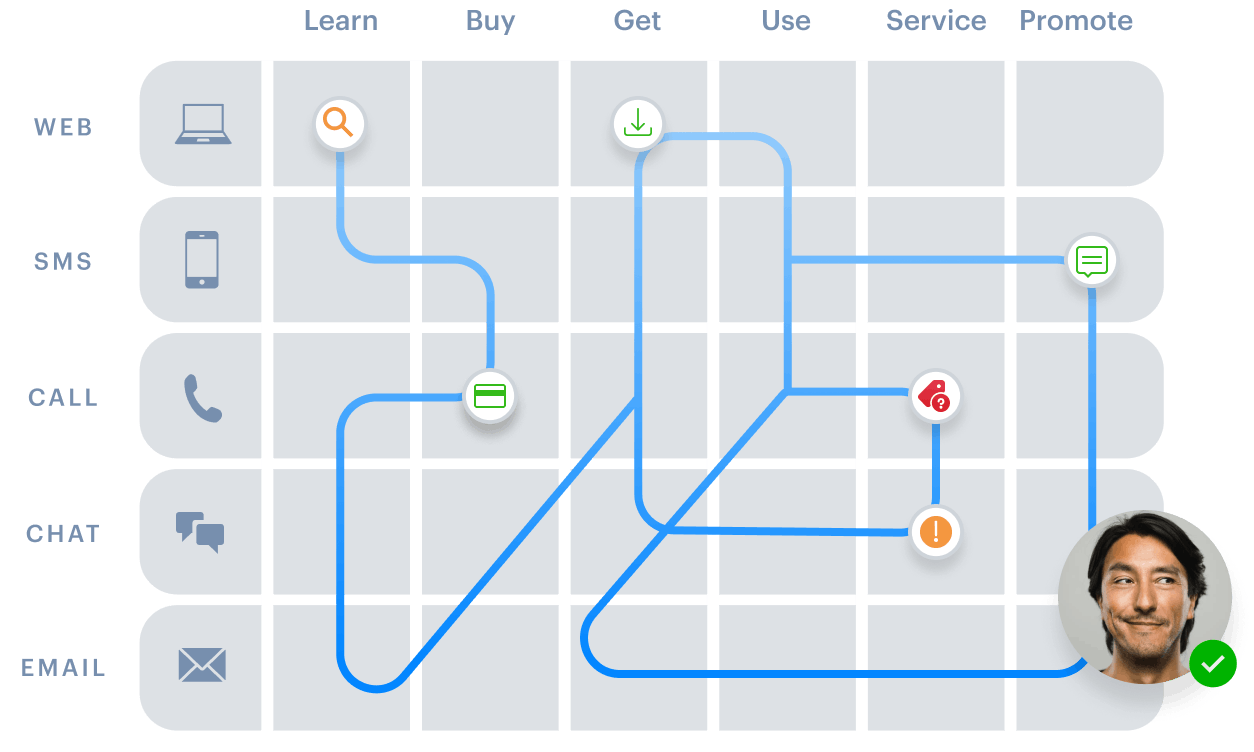
Effective customer journey orchestration involves communication with other systems for event ingestion, customer data lookup and audience activation. Medallia Experience Orchestration has you covered with application connectors, an API framework and mobile SDKs to communicate with all of your internal and external data sources and system